With Google Apps not allowing free signups anymore, I was looking forward to using Outlook to handle the email services of my yet-to-launch websites – apart from that I don’t really use any Outlook account for any communication purposes. But if you use Outlook for your business or if your Outlook email is used to sign into you social accounts, this is something you need to worry about. Christy Philip Mathew has uncovered something that might prevent you from using Outlook anymore.
The Vulnerability
When you log into a website, a cookie is sent from the website and stored into your system. This cookie contains the session information related to the website. The website can read the cookie, validate and invalidate it. This is done to prevent yourself from logging in again if you are using any other Microsoft service just like how you don’t need to log into Gmail once you have logged into Google.com. This is for the user’s convenience but can be put to wrong use also.
When you log into an email service, a cookie is stored in your browser and is invalidated once you log out of the service. But this is not the case with Outlook or Hotmail. The cookie stored in your browser remains validated even after you log out and this explains the Vulnerability we are talking about.
Demonstration
The video below demonstrates how a person can hijack your Outlook account with the help of the session cookie stored in your browser.
To test it yourself, you can follow the steps given below:
- Sign into your Outlook or Hotmail account using Mozilla Firefox.
- Export the cookie that is created after you login. You can export it using this addon. Alternatively, you can copy the code inside the cookie manually from the browser’s directory.
- Sign out of your Outlook account. The cookie should now be invalidated – but it’s NOT.
- Import the cookie that you had exported in Step 2. You can import the cookie using this addon.
- Open outlook.com in a new tab and you should see that you are automatically signed into the email service.
Though you can sign into your account using the cookie you imported, you will have to re-enter your password to change it. Some other highly sensitive options require re-authorization which means that in case your account gets hijacked using this method, your password will not be compromised
But there is a lot more a hacker can do with the help of this vulnerability. A few tasks include – reading and deleting your emails, backing them up or forwarding them, changing the passwords of social accounts that are connected with your Outlook email and a lot more.
Microsoft’s Response
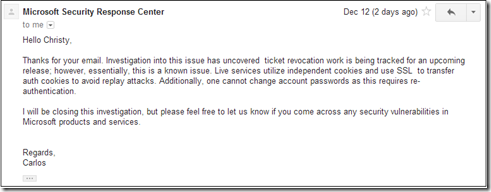
Christy contacted Microsoft’s security team regarding this and the reply from them can be seen below:
Microsoft Security team decided to close the ticket saying that the account’s password can not be changed. Looks like they are not cautious about the seriousness of the vulnerability. Perhaps they might fix this in their next release. It if after receiving this response that Christy chose to disclose it publicly.
Implementation Methods
Account Hijacking using this cookie vulenrability is possible using the following ways:
- Physical access to your computer: If a person has access to your computer, he can follow the steps I have mentioned above and store the cookie safely to access your account in future using any other machine and at any time!
- Malwares: You must be aware of Malwares spreading a lot these days via social networks like those that replicate the antivirus program on your PC. These malwares can send the cookies to the hacker via the Internet.
- Session Sniffer: A sniffer is a packet analyzer that can intercept and log traffic passing over a digital network. These programs can be used to sniff sessions over a LAN/WiFi network. An example of this is dSploit. Whatspapp sniffer that can read messages sent via Whatsapp over the same network uses the same concept because Whatsapp does not encrypt messages while they are sent.
Unfortunately, there is nothing you can do to prevent your account from being hijacked because you do not have the authority to invalidate the cookie after you log out. What are your thoughts regarding this?
Thanks Christy
via The Hacker News